Someone bought 30 legitimate WordPress plugins, waited eight months, then turned them into a malware operation. Millions of sites were affected. The attack was invisible until it wasn’t.
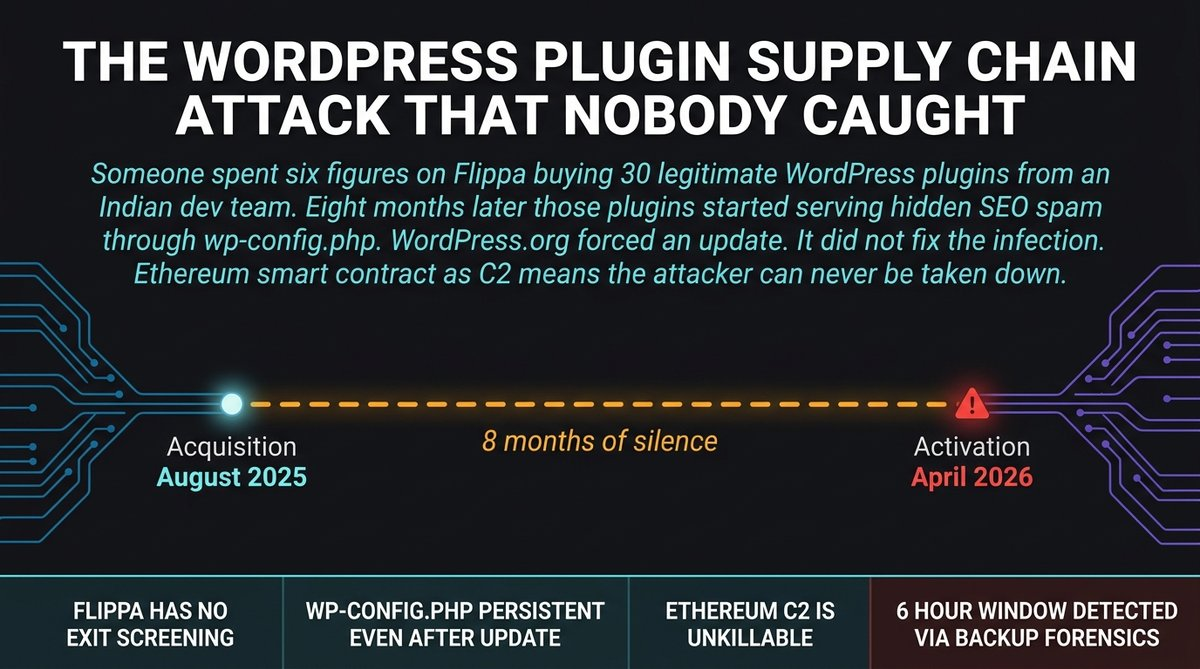
A developer published a forensic breakdown this week that is now making the rounds in security circles. The details are specific and disturbing. Someone going by “Kris” bought a portfolio of free WordPress plugins from an established Indian dev team on Flippa for six figures. Eight months after the sale, those plugins started serving hidden SEO spam to Googlebot through a backdoor that used an Ethereum smart contract as its command-and-control server. WordPress.org force-updated the plugins to stop the phone-home. But the infection in wp-config.php kept running.
The HN thread hit 545 points in five hours. The security community noticed. They should.
Here’s the thing: this was not a hack in the traditional sense. Nobody broke into a server. Nobody exploited a zero-day. Someone bought a legitimate business, waited for trust to compound, then used it as a delivery mechanism for malware. The supply chain attack trap is invisible until it springs.
The attacker acquired 30-plus plugins from WP Online Support and Essential Plugin on Flippa. These were real products. Some were 10 years old. Hundreds of thousands of downloads. The original developers had no idea what would happen post-sale. They sold to whoever paid. That is how Flippa works.
The backdoor was planted on August 8, 2025, in version 2.6.7. The changelog said “Check compatibility with WordPress version 6.8.2.” The actual change was 191 lines including a PHP deserialization RCE that sat completely dormant for eight months before activating on April 5-6, 2026.
Eight months of silence. That is the part that should worry you.
If you are running WordPress and you think the plugin ecosystem is safe because WordPress.org reviews updates, this attack should change your mind. The malware was invisible to site owners. It only served hidden content to Googlebot. You would have seen a normal site. Your WordPress dashboard showed no infection. The only alert came from WordPress.org’s plugin team, which fired after the forced update was already in progress.
But here is the real kicker: the forced update did not clean the infection.
WordPress.org v2.6.9.1 neutralized the phone-home mechanism. But it left wp-config.php untouched. The SEO spam was still serving to Googlebot. The analyst had to use backup forensics, comparing file sizes across eight snapshots, to figure out when the injection happened. They pinpointed it to a six-hour 44-minute window on April 6, 2026, between 04:22 and 11:06 UTC.
That is the gap between “patched” and “actually clean.”
But wait: the Ethereum command-and-control is the part that should make every security team lose sleep tonight.
The malware resolved its phone-home domain through an Ethereum smart contract. Traditional takedowns do not work on smart contracts. You cannot seize a smart contract. You cannot get a registrar to take it down. The attacker can point to a new server by updating the contract at any time. Gas fees are a few dollars. The infrastructure is permanent unless you convince the Ethereum network to hard fork.
This technique is not theoretical. It is deployed. The attacker paid a few dollars in gas to make their command-and-control unblockable. That is the real innovation here, and it is going to spread to every malware operation that can afford a wallet address.
If you are running WordPress right now, here is what to check. Look at your wp-config.php file. Look for anything you did not add yourself. If you have plugins from the WP Online Support or Essential Plugin portfolios, assume they were all affected unless you have verified otherwise. The force-update stopped the phone-home. It did not remove the injection.
The larger lesson is not technical. It is about trust. You trusted that the plugins you installed were built by the people whose names were on them. Some of those people sold their businesses to someone who used that trust to inject spam into your site. The supply chain runs on reputation. Reputation can be bought and sold with no verification.
WordPress.org cannot screen every Flippa transaction. The original developers did not know. There is no exit interview for plugin sales. The moment you sell your plugin business to a stranger, you have lost control of your supply chain, and the millions of sites running those plugins are along for whatever ride the new owner decides to run.
Check your configs. Run a forensic comparison if you can. The eight-month sleeper was clever. The next one might not wait that long.
Sources:
– Anchor.host Forensic Writeup
– Hacker News Discussion